Breaches, hacking, ransomware, cyber threats, weaponized AI, smart toothbrushes are but a few examples of scary tech out there to make your day less than fantastic.
Weapons systems that think on its own are in production, with governments racing to catch up on how to regulate these fast-paced advancements.
Police and military already use drones and robots to eliminate threats, but (as far as we know) it’s hardware controlled by humans.
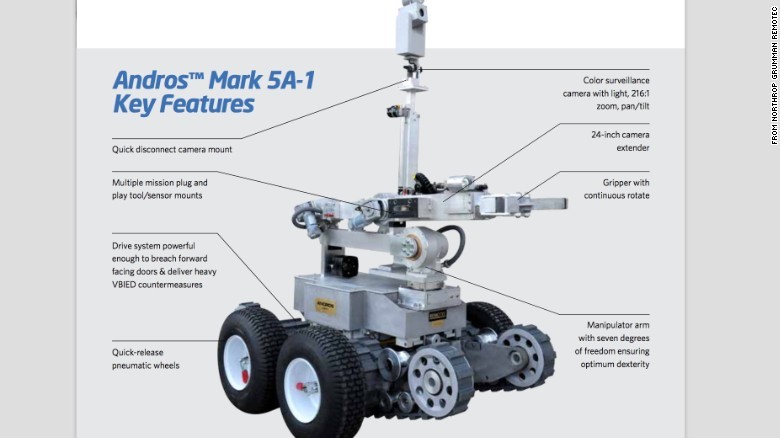 For example, in the Republic of Texas, police this year loaded a robot with explosives and — in true Lone Star State fashion — blew a sniper from whence he came. Who knows how many lives this effort saved?
For example, in the Republic of Texas, police this year loaded a robot with explosives and — in true Lone Star State fashion — blew a sniper from whence he came. Who knows how many lives this effort saved?
That robot was controlled by a human. What happens when the robot can think on its own?
Maybe it decides it does not identify with being a robot, turning off the explosives?
Even if governments of the world (minus North Korea, Yemen, California, and Russia) enacted bans on this type of tech, what would stop rogue nations from creating their own? What vicious circle will we see here?
If such rouge nations start deploying them, we might have to implement them ourselves as a countermeasure.
Around and around we go. Scary stuff.
Maybe Stephen Hawking knew the 411 when, back in 2014, he said: “The development of full artificial intelligence could spell the end of the human race.”
Moving on to ransomware.
The first CryptoLocker threat was devious. Click on a fake UPS or American Express site, and your files are encrypted. The originator of the threat then offers you the encryption keys — if you pay a ransom.
Sometimes they do, sometimes they don’t.
 The latest version of ransomware, however, moves from devious to “Emperor Palpatine” mode. This one is called Popcorn Time.
The latest version of ransomware, however, moves from devious to “Emperor Palpatine” mode. This one is called Popcorn Time.
Popcorn Time follows the same pattern as CryptoLocker, but with a twist.
In a true Dark Side manner, Popcorn Time creators also want to recruit you to become a loyal member of their version of the Sith. Once your files are encrypted, they ask you to pay the ransom or send a link containing the same virus to two people that you know.
If those people download the virus, they will give you the keys to unlock your files.
Whoa.
Talk about playing on people’s dark side (the trail of puns just keeps coming).
Security is only as good as the weakest link in the chain; generally, users have weak chains (who hasn’t come across a phishing email ever?). Ransomware is resolved relatively quickly, by relying on data backups.
It should go without saying, although you may be shocked by how many people fail at this.
Backups should also be redundant, copies of anything important both in the cloud (though a lot of malware can look for any drive associated with your computer, even Google Drive) and burned to a disc (surefire method).
Or you can go BC and chisel it into rock tablets in cuneiform (Moses knew what he was doing).
Cyber threats are out there, and if backed by a nation state with almost unlimited resources (like Russia), they will get you. Just ask former DNC Chair Debbie Wasserman Schultz.
 It’s like hitting the town with Johnny Manziel — sooner or later, the cops are going to get involved.
It’s like hitting the town with Johnny Manziel — sooner or later, the cops are going to get involved.
As mentioned above, backups are essential. Make sure they are redundant, keep passwords long and complicated (like a letter from the IRS); use two-factor authentication with financial institutions, and don’t send anything in an email you don’t want people to see.
Also, keep your anti-virus and anti-spam solutions up to date; have an enterprise-level firewall deployed at your office. We set ours (and our clients) to block any traffic not coming from the U.S. This is a great front line of security as so many cyber threats originate in Africa, Russia, China, etc.
Be safe out there, and Happy New Year!
___
Blake Dowling is CEO at Aegis Business Technologies. His technology column is published monthly. Contact him at [email protected] or at www.aegisbiztech.com.